Experience Using Digital and Analog Multimeters
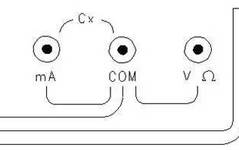
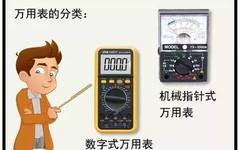
A multimeter is a versatile measuring tool that can measure voltage, resistance, current, capacitance, and short circuits, among other functions. The usage methods of different multimeters are generally similar. By mastering the principles, one can easily understand them. Below, I will demonstrate how to use a digital multimeter. Which is better, an analog multimeter or … Read more