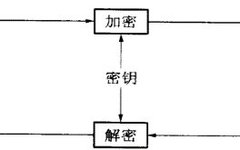
Understanding Common Encryption and Decryption Algorithms
This article is an excellent piece from the Kuanxue Forum. Author ID on Kuanxue Forum: Awei IntroductionTo engage with cryptography before analyzing ransomware, some algorithms are indeed too complex, and my brother finds it quite challenging, so I won’t embarrass myself. There may also be unnoticed errors, and I hope everyone can point them out … Read more