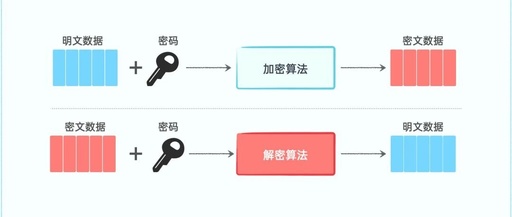
Symmetric Key Encryption Algorithms
1. AES (Advanced Encryption Standard) Core Principles 128-bit key: 10 rounds 192-bit key: 12 rounds 256-bit key: 14 rounds Block Cipher: The plaintext is divided into fixed-length blocks (blocks) for encryption. The block length of AES is fixed at 128 bits (16 bytes) Key Length: Supports128-bit, 192-bit, and 256-bit key lengths, corresponding toAES-128, AES-192, AES-256. … Read more