The currently most active AR (Augmented Reality) mobile game Pokémon Go has surpassed 15 million downloads worldwide. This “phenomenal” app, developed jointly by Nintendo, Pokémon Company, and Google Niantic Labs, combines AR technology with LBS (Location-Based Services) technology, providing players with an unprecedented gaming experience. Pokémon Go has gained immense popularity and social influence in the market, quickly becoming the most popular game on both Android and iOS platforms.
Pokémon Go is a game where players explore, capture, battle, and trade Pokémon that appear in the real world. Players can discover Pokémon in the real world through their smartphones, capturing and battling them. Currently, the application has officially launched in 27 countries including the United States, New Zealand, and Australia. The Chinese region is still in a state of IP + GPS dual-lock.
With the popularity of Pokémon Go, the security issues brought by this app have also attracted increasing attention. This article provides a brief introduction and analysis of the security risks faced by Pokémon Go and offers some safety recommendations.
1. Risk of User Information Leakage
Users who log in with their Google accounts face privacy leakage risks.
The initial version of the game allowed players to log in using their Google accounts directly, and during the login process, users would not receive any prompts regarding the app’s access permissions to their Google accounts. However, if users log in to their Google accounts and check the permissions granted to the app, they will find that the app has “full access” to their Google accounts.
The official Google help page explains “full access” as:
“If you grant an application full access to your Google account, it means that it can modify almost all information about your Google account.”
Let’s see what permissions Niantic will obtain if you log in to Pokémon Go using your Google account:
(1) Browse all your Gmail emails
(2) Send emails on your behalf
(3) Access and delete all your Google Drive files
(4) View your search history and your map navigation history
(5) Access any private photos stored in Google Photos
(6) Various other information
Additionally, if users use Gmail as the authentication mechanism for user authorization (for example, changing the password), Niantic may also have a high likelihood of obtaining access to your accounts on other websites. Of course, the possibility of Niantic planning to conduct global personal information theft is low; this vulnerability may simply be a result of oversight. We do not know the specific details, and the official statement has addressed this issue, releasing an updated version (version 1.0.1) of Pokémon Go for the first time regarding this matter.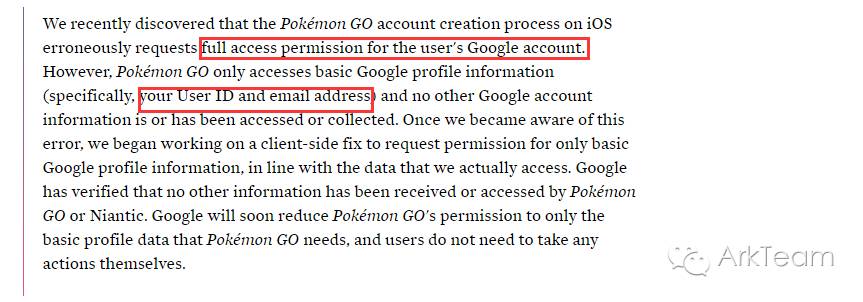
In the statement, the official acknowledged the above issues and stated that Niantic would only obtain the most basic information from users’ Google accounts. Google has also confirmed that Niantic did not obtain any information other than the user’s ID and email address.
Whether or not it is true as Niantic and Google claim, Pokémon Go indeed has full access to users’ Google accounts, which undoubtedly poses a significant security threat to those users who have not updated the app in this era of frequent information leaks.
2. Malware Threats
Downloading Pokémon Go from untrusted third-party markets exposes users to malware threats.
The global popularity of Pokémon Go has made this app a target for attackers. Although Pokémon Go has officially launched in 27 countries worldwide, for those who are unable to download the game from official app stores, downloading from untrusted third-party app markets has become a choice for many, which also provides opportunities for attackers to launch attacks.
Researchers at Proofpoint have discovered infected Pokémon Go APKs. This APK contains a malicious tool called DroidJack (also known as SandroRAT), which can attack Android devices and plant a backdoor for attackers. DroidJack is a remote control tool that allows attackers to fully control the victim’s phone. This remote control tool has been reported by security companies such as Symantec and Kaspersky in the past. Although this malicious APK has not been widely downloaded, its upload time was only 72 hours after the official launch of Pokémon Go in New Zealand and Australia.
The following image shows the login interface of the malicious Pokémon Go application, which is identical to the legitimate Pokémon Go application’s login interface, making it nearly impossible for users to discern that they have installed a malicious application.

Malicious APK login interface

Legitimate APK login interface
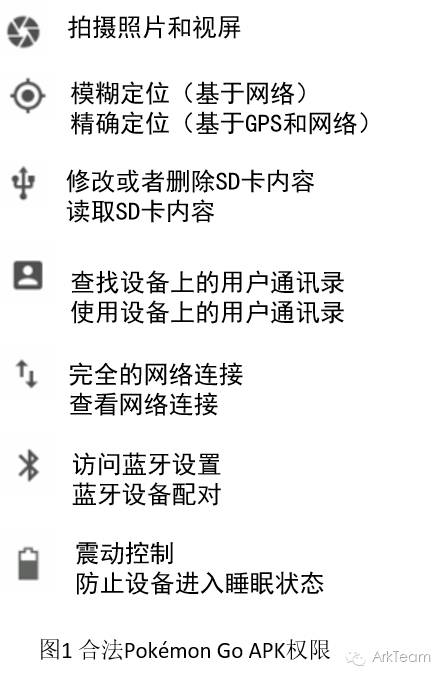
There are currently two ways to determine whether the Pokémon Go app downloaded from third-party Android markets is malicious.
The first way is to check the APK’s SHA256 hash value.
The SHA256 hash value of the legitimate APK is as follows:
8bf2b0865bef06906cd854492dece202482c04ce9c5e881e02d2b6235661ab67
The SHA256 hash value of the malicious APK that has been analyzed so far is:
15db22fd7d961f4d4bd96052024d353b3ff4bd135835d2644d94d74c925af3c4
The second way is to check the permissions of the installed Pokémon Go app. Figure 1 shows the permissions of the legitimate APK. Figure 2 shows the permissions of the APK containing the DroidJack malware, which has additional permissions on top of the basic permissions (Figure 1).
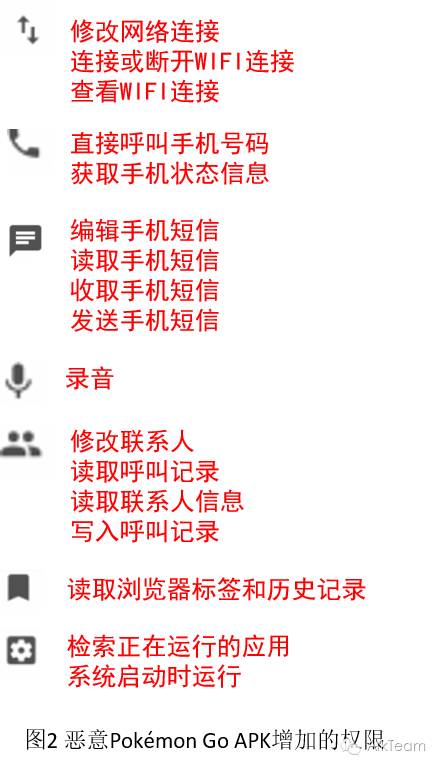
Further analysis has revealed that the version of Pokémon Go embedded with DroidJack has three additional packages compared to the legitimate version:
a
b
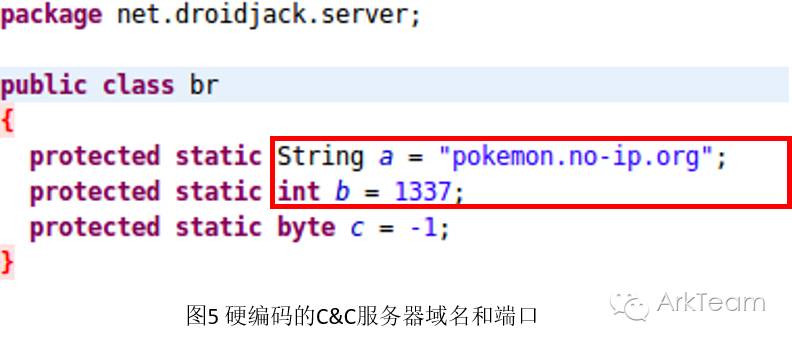
net.droidjack.server


The DroidJack remote access tool is configured to communicate with a C&C server at the domain pokemon.no-ip.org via port 1337. This domain is bound to a dynamic IP address and points to a NO-IP.org site in Turkey. This site has also been exploited by attackers in the past to cover up malicious software operations.
Although this malicious APK has not spread widely, it does indicate that cyber attackers can use Pokémon Go to lure users worldwide into installing their malicious software, thereby committing widespread cybercrime.
3. User Personal Safety
The location-based gaming approach may lead to many unexpected safety issues.
Pokémon Go is based on Google Maps to implement location-based service-related functions, and the map displayed in the game is associated with the real world. The game map is generated based on real-world maps, with slight simplifications, and the character’s position in the game is determined by the player’s geographic information in the real world. It can be said that the world in the game is an abstraction and mapping of the real world.

The location-based gaming approach of Pokémon Go is undoubtedly one of its most attractive features, as it focuses on interaction and communication between people. However, some settings in the game can easily be exploited by criminals.

A public statement from the police department in O’Fallon, Missouri, revealed that four suspects allegedly used Pokémon Go to commit robbery. These four suspects marked PokéStops in Pokémon Go to lure players into traps and then carried out their robberies.
Recently, two incidents were reported in Orlando, USA, where users were robbed while playing Pokémon Go due to neglecting their surroundings.
The gaming approach of Pokémon Go, while promoting interaction between people, also presents many uncertain threats to the personal safety of its users.
Note: There are two types of locations in the game that attract player gatherings:
Gyms: Gyms are asynchronous PVP (players versus players) areas where Pokémon gyms are generally located at major tourist attractions in cities. In gyms, players can challenge opposing Pokémon or train their own Pokémon. Players need to choose their allegiance from the three factions: “Red”, “Yellow”, or “Blue”. Players aim to occupy as many gyms as possible for their faction to gain more resources, which is why gyms often attract many players.
PokéStops: PokéStops randomly appear anywhere on the game map (generally found in parks, supermarkets, or other busy places) and correspond to real-world landmarks. PokéStops refresh items after a certain period, allowing players to obtain items for free, thus attracting a large number of players.
4. Safety Recommendations
Based on the above safety threats, the following safety recommendations are proposed:
(1) Users who log in with their Google accounts should download and use the latest version of Pokémon Go (version 1.0.1) and log in to their Google accounts to check the game’s authorization status.
(2) Avoid downloading Pokémon Go applications from third-party app markets with unknown sources. It is best to wait for the game to officially launch in your area and download the app from the official app market. Users can set up alerts on the website “Is Pokémon Go Available yet?” for official launch notifications.
(3) Players should avoid going to areas with unclear safety conditions while playing the game.
5. Conclusion
Pokémon Go, this phenomenal application, has sparked waves of enthusiasm worldwide, but we must remain calm and pay attention to the security issues it presents, considering and protecting our personal information security, privacy security, and even personal safety while enjoying the fun of the game.
References
http://www.theatlantic.com/technology/archive/2016/07/pokemon-go-is-a-no-go-for-security/490865/
https://www.proofpoint.com/us/threat-insight/post/droidjack-uses-side-load-backdoored-pokemon-go-android-app
http://www.freebuf.com/news/109023.html
http://www.theverge.com/2016/7/10/12142434/pokemon-go-armed-robberies-missouri
For more exciting content, please follow:
1. ArkTeam Official WeChat— Public account name: ArkTeam

2. ArkTeam Official Weibo:
Nickname: ArkTeam
Website: http://www.weibo.com/arkteam
