
This article continues to introduce the Hillstone Application Delivery Controller (ADC) technical case, sharing it for collective learning.
This case comes from the 【Hillstone Documentation Center https://docs.hillstonenet.com.cn/】, and I recommend everyone to explore the technical treasures within.
This section introduces how to configure the security policies of the ADC device to restrict internal network access to the external network, achieving domain-based access control.
Deploying the ADC at the Internet exit, when controlling internal network traffic access through its security policies, aims to reduce the high operational costs caused by frequently changing destination addresses by implementing domain-based access control based on the destination domain names accessed by internal network users. Currently, the ADC supports domain-based access control for HTTP and HTTPS traffic.
1. Networking Scenario
Enterprises deploy ADC devices at the Internet exit. For enterprises, while allowing employees to access certain websites using the corporate internal network, it is also necessary to prohibit access to other websites. Taking the websites “www.test1.com” and “www.test2.com” as examples, security policies need to be configured on the ADC to achieve:
- Allow corporate employees to access “www.test1.com”.
- Block corporate employees from accessing “www.test2.com”.
The topology diagram is as follows:

2. Configuration Approach
Ensure that the exit gateway of the corporate internal network clients points to the ADC, and perform the following configurations on the ADC:
- Security Policies: Create two security policy rules, both bound to applications HTTP and HTTPS, to prevent other application traffic from matching the above rules.
- One rule allows HTTP/HTTPS traffic to access “www.test1.com”, i.e., allowing corporate employees to access “www.test1.com” via HTTP or HTTPS;
- The other rule blocks HTTP/HTTPS traffic to “www.test2.com”, i.e., prohibiting corporate employees from accessing “www.test2.com” via HTTP or HTTPS.
Before configuration, please ensure the following preparations are completed:
- The device is operating normally, and you can log in to the WebUI management device through the configuration management IP;
- All links are reachable across the network;
- Configure SNAT according to actual conditions.
3. Configuration Steps
Step 1: Configure Interfaces.
Configure the device’s ethernet4/5 interface as the internal network side interface; ethernet4/4 interface as the Internet exit interface.
1)Select “Network > Interfaces”, choose the ethernet4/5 interface and click “Edit”.
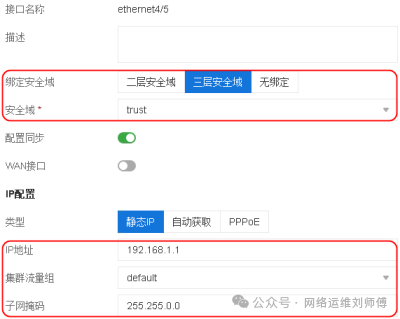
- Bind Security Domain: Layer 3 Security Domain
- Security Domain: trust
- IP Address and Subnet Mask: 192.168.1.1/16
- Other options remain at default values
2)Select “Network > Interfaces”, choose the ethernet4/4 interface and click “Edit”.

- Bind Security Domain: Layer 3 Security Domain
- Security Domain: untrust
- IP Address and Subnet Mask: 202.1.1.1/16
- Other options remain at default values
Step 3: Configure Security Policies for Domain-Based Access Control of Internal Network Traffic.
In this example, to allow corporate employees to access “www.test1.com” and prohibit access to “www.test2.com”, create two security policy rules and specify the above two domain names as matching conditions for the two rules.
If there are many domain names that need to be controlled, users can first add them to the domain book and then specify the corresponding domain book for the security policy rules; alternatively, specify wildcard domain names for the security policies.
1)Create a security policy to allow corporate employees to access “www.test1.com”.
Select “Network > Security Policies > Policies”, and click “New > Policy”.

- Name: rule1
- Domain: Click the “+” button, then select “Domain” from the dropdown menu and enter “www.test1.com” in the text box
- Action: Allow
- Options
- Log: Select “Session Start” and “Session End”
- Other options remain at default values
2)Create a security policy to block corporate employees from accessing “www.test2.com”.
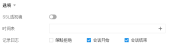
Select “Network > Security Policies > Policies”, and click “New > Policy”.
- Name: rule2
- Domain: Click the “+” button, then select “Domain” from the dropdown menu and enter “www.test2.com” in the text box
- Action: Deny
- Options
- Log: Select “Policy Deny”
- Other options remain at default values
Step 4: Configure Monitoring.
To view the session logs generated by the security policy rules “rule1” and “rule2”, in addition to enabling the logging feature for the rules, the device’s session logging feature must also be enabled.
Select “Monitoring > Logs > Log Management”, and click the button for session logs.
button for session logs.

- Enable: Click the “Enable” button
- Log Username: Click the “Enable” button
- Log Hostname: Click the “Enable” button
- Other options remain at default values
4. Result Verification
Taking the example of corporate employees accessing “www.test1.com” and “www.test2.com” via HTTP, check the session logs generated on the ADC to determine whether the access was successful.
- When accessing http://www.test1.com, on the ADC device, select “Monitoring > Logs > Session Logs” to view the corresponding session logs. As shown below, corporate employees successfully accessed http://www.test1.com.

- When accessing http://www.test2.com, on the ADC device, select “Monitoring > Logs > Session Logs” to view the corresponding session logs. As shown below, corporate employees failed to access http://www.test2.com.

–End–
