1. Introduction
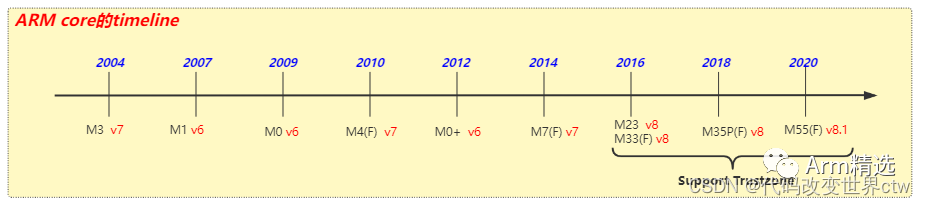
The Cortex-M processor series is based on the M-Profile architecture, providing low-latency and highly deterministic operations for deepembedded systems. Our latest generation Cortex-M processor is the Cortex-M55. The Cortex-M55 is the first processor based on the Armv8.1-M architecture, utilizing the vector processing extension Arm Helium technology. The Cortex-M55 brings higher levels of machine learning andsignal processing performance to the next generation of small embedded devices (including wearables, smart speakers, etc.).
The Cortex-M processors are designed to support the microcontroller market
-
Based on RISC architecture, most instructions are executed in a single cycle
-
Programming is simpler—entire applications can be programmed in C language
-
Requires fewer features than Cortex-A
Registers and ISA variations of other ARM cores
-
Uses Thumb instructions, does not support the ARM instruction set (i.e., does not support A32, does not support A64)
-
Only SP is banked in the general-purpose registers
-
Two operating modes: Thread mode and Handler mode
Different modes and exception models
-
Only two execution modes: Thread and Handler modes
-
The vector table consists of addresses and does not contain instructions
-
Exceptions automatically save state (R0-R3, R12, LR, ReturnAddress, RETPSR) on the stack
Different system control/memory layout
-
The core has a fixed memory mapping
-
No coprocessor C15 – controlled by memory-mapped control registers (MRS, MSR)
ARMv8-M is a 32-bit load/store architecture
-
The only allowed memory accesses are load and store
-
Most internal registers are 32 bits wide
Programming model
Two modes: Thread mode and Handler mode, with two execution levels in Thread mode: privileged and Unprivileged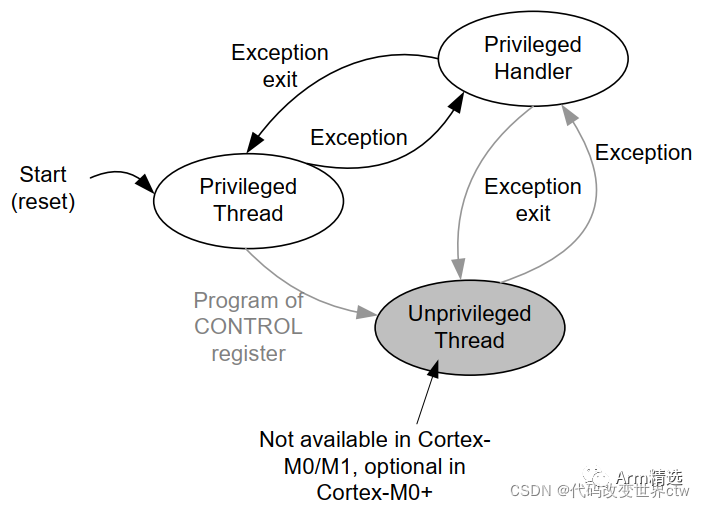
2. Registers
2.1 Summary of Registers
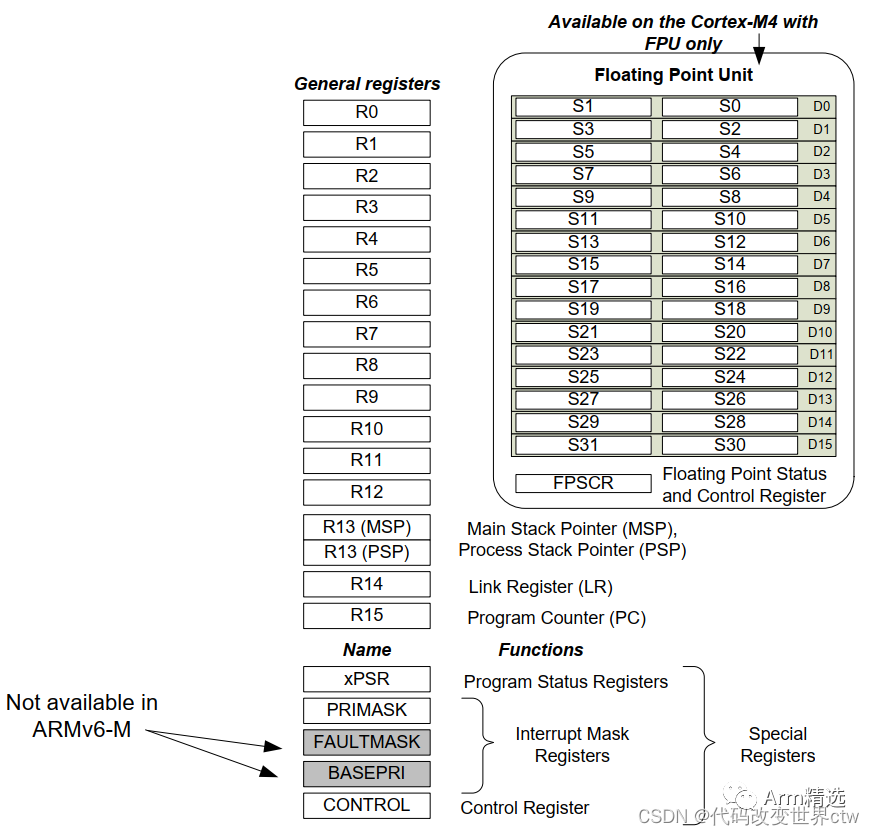
2.1.1 General-purpose registers (all are 32 bits)
-
R0-R12 (Rn).
-
R13 stack pointer (SP).
-
R14 link register (LR).
-
R15 program counter (PC)
2.1.2 Special registers
-
Mask (MASK) registers:
(1) Exception mask register: PRIMASK
(2) Priority mask register: BASEPRI.
(3) Fault mask register: FAULTMASK
-
Control register: CONTROL
-
Two stack pointer limit registers: MSPLIM and PSPLIM
-
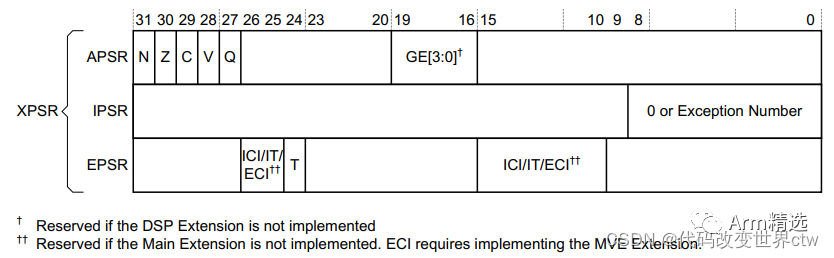
Program status register: Program Status Register (XPSR), includes:
(1) Application Program Status Register (APSR).
(2) Interrupt Program Status Register (IPSR).
(3) Execution Program Status Register (EPSR)
2.1.3 Memory-mapped registers
In addition, there are some memory-mapped registers
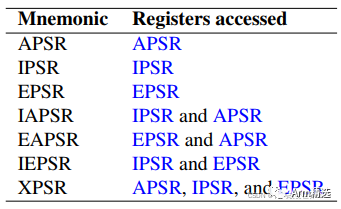
2.2 Introduction to XPSR, APSR, IPSR, and EPSR
msr、mrs can be segmented to access these registers
2.2.1 Interrupt Program Status Register (IPSR)
-
When PE is in Thread mode, IPSR value is 0
-
When PE is in Handler mode,
(1) When an exception occurs, IPSR saves the exception number being handled
(2) When calling from Secure state to Non-secure state, IPSR value is 1
-
Using MRS instruction to forcibly modifyIPSR, will not take effect
2.2.2 Execution Program Status Register (EPSR)
Mainly the EPSR.T bit
-
0 – Any instruction will produce INVSTATE error or HardFault
-
Instruction set uses T32
2.3 CONTROL register
-
Only Privileged execution state can write to the control register, both Privileged and unPrivileged states can read the control register.
-
This architecture requires a Context synchronization event to ensure visibility of changes to the CONTROL register
-
When an exception enters or exits, hardware automatically modifiesCONTROL.SPSEL, when PE is in Thread modeCONTROL.SPSEL can be used to select the stack pointer
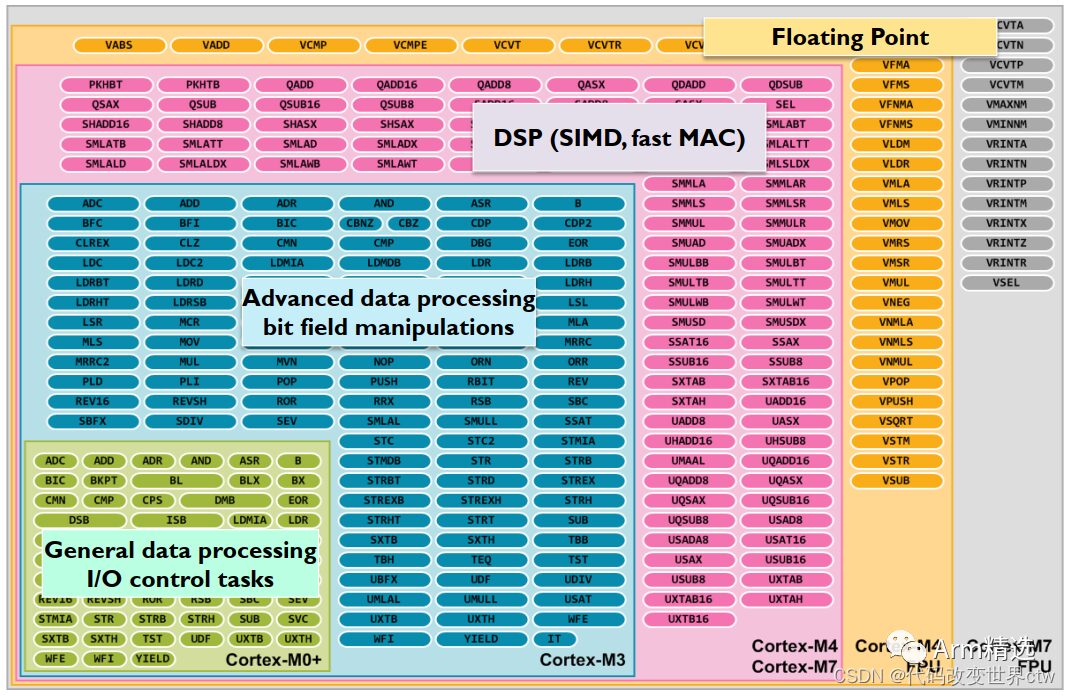
3. Instruction Set ISA
All Cortex-M processors support an instruction set called Thumb. When Thumb-2 technology is available, the complete Thumb instruction set becomes quite large when extended. However, different Cortex-M processors support different subsets of instructions available in the Thumb ISA, as shown in the following figure:
4. Secure State
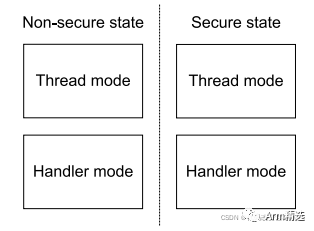
-
If security extensions are implemented, memory regions and other critical resources marked as secure can only be accessed when the PE is executing in secure state
-
If security extensions are implemented, during Cold reset and Warm reset, the PE will enter Secure state
-
If security extensions are implemented, during Cold reset and Warm reset, the PE will enter NON-Secure state
If security extensions are implemented, the following registers are banked by security:
-
R13 (SP) in general-purpose registers
-
Special registers: MASK registers (PRIMASK, BASEPRI, FAULTMASK), CONTROL register, stack pointer limit registers (MSPLIM, PSPLIM)
-
System Control Space (SCS)
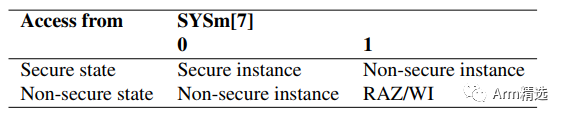
MRS and MSR instruction encoding’s bit[7] indicates which group of registers is being operated on (Secure or NON-Secure)
Comparison of cortex-A Trustzone and cortex-M Trustzone:
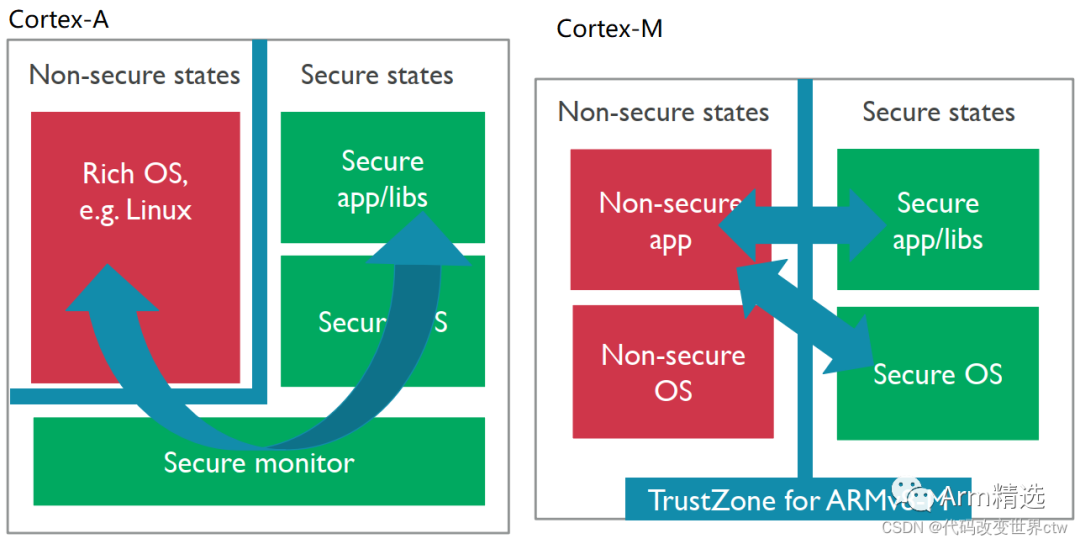
On cortex-M, switching between dual systems uses the Secure Gateway (SG) instruction, but SG can only be called in special memory, even if NSC (non-secure callable)
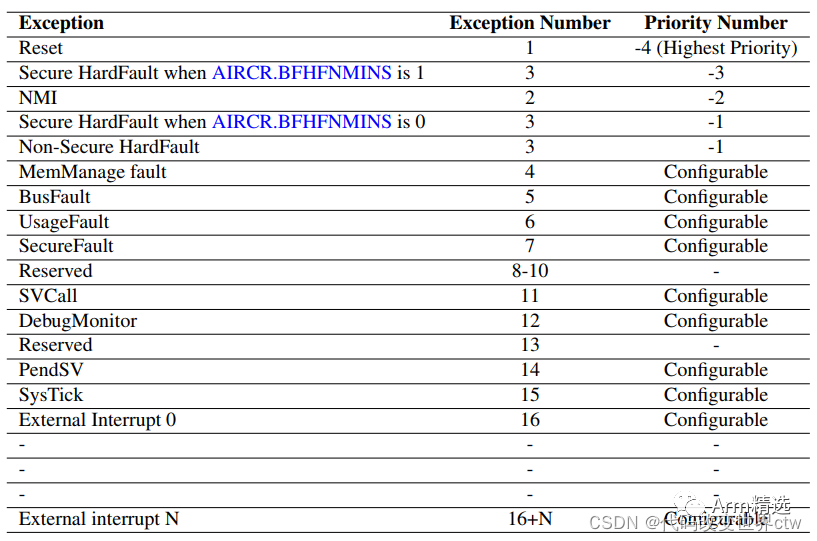
5. Exception Numbers and Exception Priorities
A Nested Vectored Interrupt Controller (NVIC) interrupt controller is built into the cortex-M
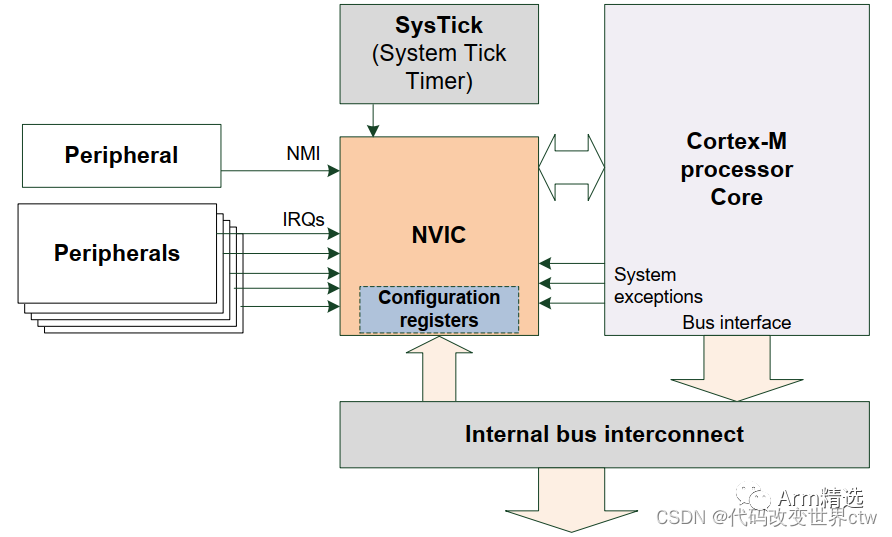
The exceptions and interrupts of cortex-M have the following priorities