As we all know, embedded systems are widely used in today’s intelligent industries, but embedded systems often contain sensitive information and perform critical functions.
These systems may involve sensitive information such as personal privacy, commercial secrets, or national security. Once attacked, it can lead to serious consequences. The network security of embedded systems is designed to prevent unauthorized access that could lead to data breaches, tampering, and other security issues.
Next, let’s comprehensively understand the network security issues of embedded systems.
Ways to Threaten Network Security
1) Malware Attacks: Malicious software may exploit system vulnerabilities to deploy malware, intercept or tamper with system data, and control or damage the system.
2) Unauthorized Access: Unauthorized access to embedded systems may be gained by guessing credentials (such as passwords) or exploiting system vulnerabilities.
3) Data Breaches: Sensitive data may be leaked to unauthorized third parties due to improper system configuration or vulnerabilities.
4) Human Leaks
Network Security Protection Measures
1) Strengthening System Design and Development:
Consider security requirements early in the system design phase and choose software and hardware components that comply with international or regional security standards. Utilize middleware and virtualization technology for component partitioning to enhance system security and maintainability.
2) Implementing Authentication and Access Control:
Use strong password policies, limit login attempts to prevent brute force attacks. Implement multi-factor authentication to enhance system security.
3) Data Encryption and Transmission Security:
Encrypt sensitive data for storage and transmission to ensure data security during storage and transfer. Use secure protocols (such as IPsec, SSH, SSL, etc.) to protect communication processes.
4) Regular Updates and Patch Management:
Regularly update the firmware and software of embedded systems to fix known vulnerabilities. Use vulnerability scanning tools to scan the system and promptly identify and fix potential vulnerabilities.
5) Physical Security Measures:
Ensure the physical security of embedded systems, such as using high-strength materials, electronic locks, and surveillance cameras. Harden physical interfaces (such as serial ports, JTAG interfaces, etc.) to prevent unauthorized access.
6) Continuous Monitoring and Response:
Establish a continuous monitoring mechanism to regularly check the security status of the system. Respond promptly to security incidents, including real-time alerts, log recording, and the formulation of security incident response plans.
Remote control of embedded systems refers to the technology that allows monitoring and controlling dedicated computer systems (i.e., embedded systems) embedded in other devices via network connections.
1) Wi-Fi:
Suitable for applications requiring high data transfer rates, such as smart home devices. Wi-Fi provides extensive coverage and high-speed data transfer capabilities, allowing users to conveniently control embedded systems remotely through smartphones, tablets, etc.
2) Bluetooth:
Suitable for short-distance connections, typically used for wearable devices and accessories. Bluetooth technology features low power consumption and low latency, enabling embedded systems to communicate quickly and stably with nearby devices.
3) Cellular Networks:
Suitable for mobile devices and remote monitoring applications. Cellular networks provide extensive coverage and stable connection quality, allowing embedded systems to be remotely controlled in mobile environments.
4) LoRa and Zigbee:
Suitable for low-power, long-distance transmission, commonly used in sensor networks. These technologies have low power consumption and low cost, making them suitable for applications requiring remote monitoring and control of numerous sensors.
1) Smart Home:
Users can remotely control lighting, air conditioning, curtains, and other devices in their homes through mobile applications, achieving a smart home life.
2) Industrial Automation:
Factories can optimize production processes and warn of faults through remote monitoring of equipment status. This helps improve production efficiency and reduce maintenance costs.
3) Health Monitoring:
Wearable devices can monitor users’ health data in real-time and send the information to healthcare providers. This allows users to stay informed about their health status and receive professional medical advice when necessary.
4) Transportation:
Embedded systems are widely used in traffic management, vehicle control, navigation systems, etc. Through remote control, traffic flow optimization, vehicle safety monitoring, and rapid responses to emergencies can be achieved.
5) Environmental Monitoring:
In environmental monitoring stations, meteorological stations, and water quality monitoring facilities, embedded systems can obtain and process a large number of environmental parameters in real-time. Remote control can enable real-time monitoring and early warning of environmental quality.
Currently, embedded systems, artificial intelligence, and the Internet of Things are developing rapidly, leading to an increasing talent gap in enterprises and the release of more emerging job resources.
Huaqing Vision has been deeply engaged in the high-end IT field for 20 years, carefully creating [Embedded Systems][Artificial Intelligence] high-end courses. A complete learning path helps you progress from basic to advanced, suitable for industry novices, technical transformation, cross-industry transitions, and on-the-job enhancement and other groups.
Hua Mei has prepared a learning roadmap for embedded systems and artificial intelligence and a free trial class. Contact Hua Mei to get it!

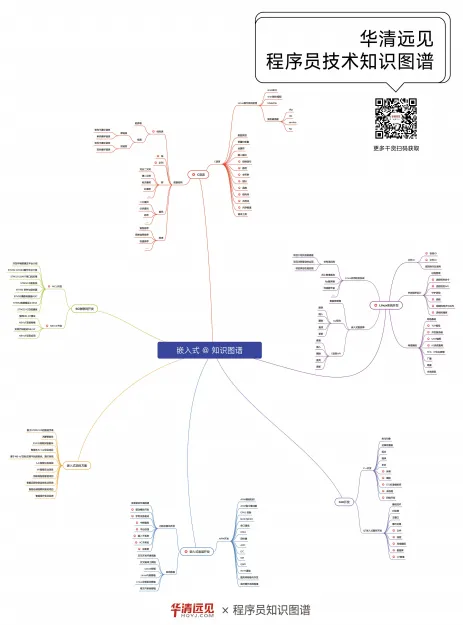
△Embedded Learning Roadmap
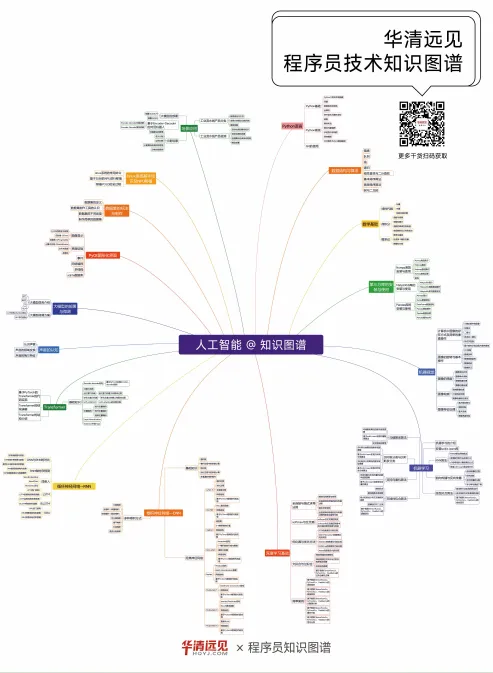
△Artificial Intelligence Learning Roadmap
👇👇👇

👇👇👇

Contact Hua Mei👩🏫
➡QQ: 2521472503
vx▼

More contact information
↓↓↓
Little Red Potato|Huaqing Vision Chengdu Center
Official Douyin|Huaqing Vision Chengdu Center
Sorry for not looking, just give a thumbs up